Review existing controls & implement missing controls


Business is continuously moving towards newer frontiers in terms of digital adoption, cloud technologies and near real time transactions make it imperative for all customer facing systems to be fully secured. Regulatory authorities i.e., government bodies appointed for various sectors focus on ensuring that businesses operating within their domain keep optimum levels of security controls deployed and functional. Some of the key industries regulated world over are Banking, Financial Services, Insurance, Government Departments, Entities processing financial information like Debit cards, Credit cards, Personally Identifiable Information, etc.
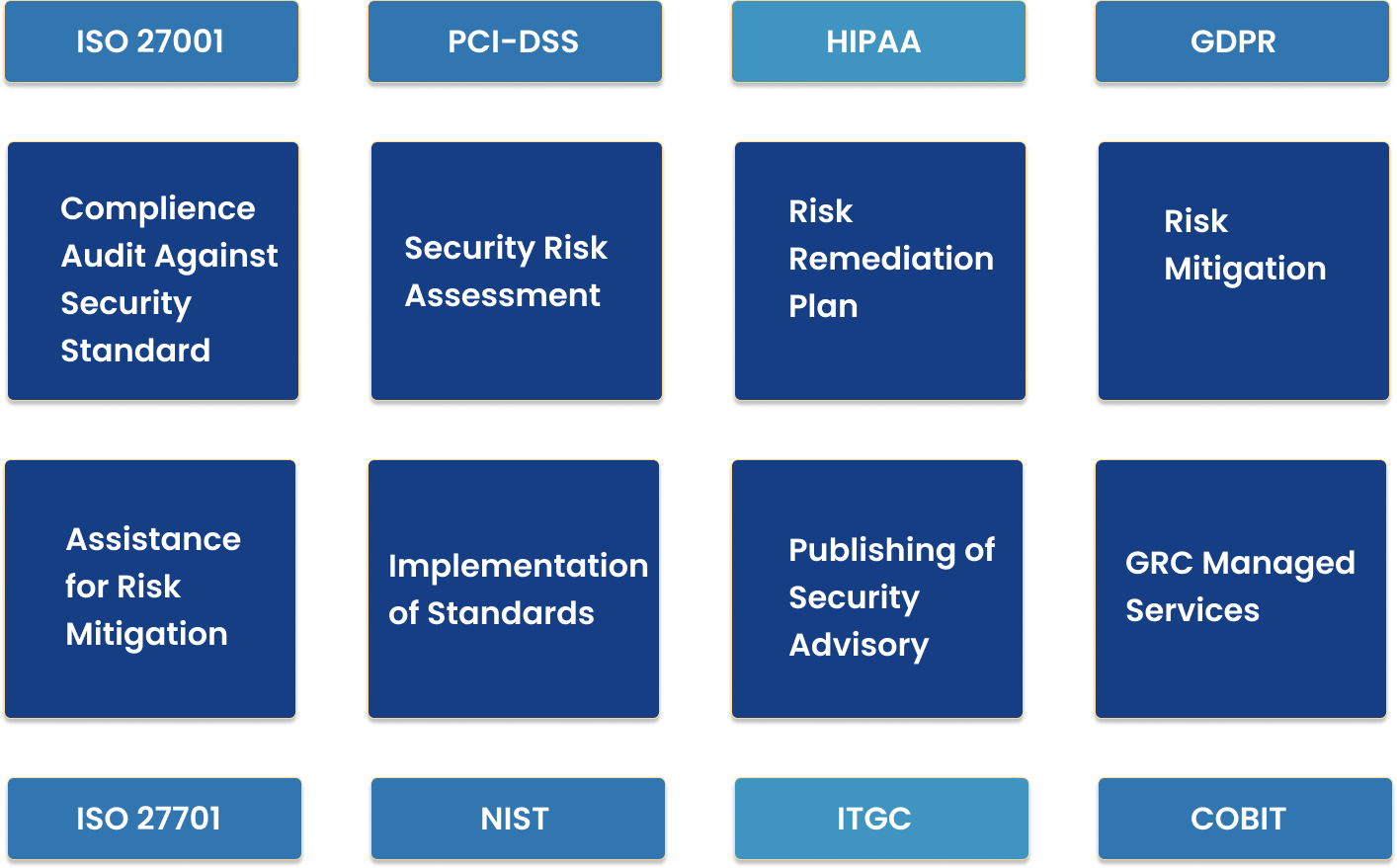
Some of the major certifications targeted by organizations to be recognized as differentiators in their domains are certifications like ISO 27001, ISO 27701, ISO 31000 and/or ISO 22301:2019. Beyond there are industry and region-specific certifications that can provide edge to a business targeting customers operating in the domain or region specifically. Some of these certifications are GDPR, HIPPA, PCI-DSS, NIST, COBIT, etc..
Following are the key steps undertaken during any compliance Audit:
Review existing controls & implement missing controls
Conduct Risk assessment & constitute mitigation plan
Create statement of applicability
Define plan for measuring effectiveness of controls
Design & implement security awareness program Operate & Monitor ISMS program
Conduct internal audit to determine readiness
Implement preventive and corrective technical, process and policy controls to meet required standards of target audit
Initiate External Audit for certification/Audit against internal policy compliance